Design insight: how to choose the right RFID reader
Across applications as varied as electric vehicle (EV) charging, secure print management, and physical access control, the right RFID reader can play a valuable role in the system’s functionality and security while promoting compliance with relevant standards.

Access control environments are more complex than ever, spanning physical and digital domains, multiple credential technologies, and evolving regulatory and security requirements. Today, RFID and mobile credential technologies such as Bluetooth® Low Energy networking and NFC play a growing role in applications for user authentication and access control for both physical spaces and digital systems. At the same time, the industry has seen an explosion in credential types and communication protocols, creating new challenges for interoperability, security and system integration.

This means that the choice of RFID reader has a big impact on the system’s flexibility and future-readiness. This six-step guide shows how to choose the best type of RFID reader for any given application.
1: Define the use case and security requirements
The first step in choosing the right RFID reader is understanding exactly how and where it will be used. Start by identifying the application: EV chargers, secure print managers, vending machines, physical access control and single sign-on systems each present different technical and security problems. In some cases, it might be necessary to integrate multiple use cases across departments or facilities, or even to merge physical and logical access into a unified solution. The reader must be flexible enough to support a range of credentials and systems through a single device, ensuring consistent security and a seamless user experience across access points.
The operating environment and the level of access control needed also have an impact. A reader used for basic office entry will have different requirements from one deployed in a healthcare facility, research laboratory or military base. Sensitive environments may require support for advanced encryption, secure communication protocols or multi-factor authentication.
2: Consider existing infrastructure and legacy systems
The next step is to assess the current infrastructure. In many cases, the RFID reader needs to fit into an existing ecosystem of ID cards, back-end software, physical devices and communication protocols. The need for compatibility with this legacy equipment can substantially affect both cost and implementation speed.
Legacy systems may use protocols such as Wiegand or RS-232, while newer systems rely on modern interfaces such as Open Supervised Device Protocol (OSDP) or USB. The right RFID reader should be able to interface with all, especially in mixed environments or during phased upgrades. Choosing a reader which bridges old and new ensures a smoother upgrade path and reduces the total cost of ownership.
The engineer should also consider the question of physical integration: will the reader need to match a specific size or housing? Does it need to be retrofitted into an existing device or panel?
3: Choose the right technologies
Credential technology is evolving quickly: readers must be able to support a wide range of formats to meet current needs and to adapt to what comes next.
A universal, technology-agnostic RFID reader gives the flexibility to bridge legacy systems, meet today’s security standards, and embrace future innovations such as mobile credentials.
There are various ways in which reader technology has evolved:
- From LF to HF RFID: legacy 125 kHz low-frequency (LF) credentials are still sometimes used in access applications, but they do not support strong encryption, and are vulnerable to cloning. Most organizations have moved to modern 13.56 MHz high-frequency (HF) card formats such as the MIFARE® DESFire® standard, which offer stronger security features and better support for regulatory compliance.
- From physical badges to mobile credentials: more organizations are moving to mobile access solutions using smartphones and wearables. Bluetooth Low Energy networking and NFC technologies enable fast, contactless authentication which enhances user convenience without sacrificing security.
- From generic mobile support to platform-native integrations: advanced mobile credentialing platforms, such as Employee Badge in Apple Wallet and Google Wallet, are rapidly being adopted in enterprise and institutional settings. These require RFID readers that can support mobile wallets natively, across devices for both iOS and Android™ operating environments.
- Standards-based credentials: highly secure, standards-based credentials, such as Public Key Open Credential (PKOC), are gaining traction. These credentials support both cards and mobile devices over NFC or Bluetooth networks, and use asymmetric cryptography to provide stronger security and future-proofing.
A universal reader supports all of the above, helping users to manage hybrid environments today while paving the way for a secure, streamlined mobile-first future. A technology-agnostic, universal reader ensures broad compatibility across both legacy and modern formats, including encrypted HF cards and advanced mobile credentials. This allows organizations to maintain continuity while planning for a secure and seamless upgrade to mobile access in the future.
4: Ensure global readiness and regulatory compliance
If a system is to be deployed across multiple regions or in regulated environments, the reader must meet all required certification requirements and security standards. Different countries have different regulations and certification schemes, and industries such as healthcare, education and government often have strict data privacy and cybersecurity requirements.
Choosing a globally certified, security-conscious reader reduces deployment friction and helps to ensure compliance wherever the system is deployed.
This means that there is great value in RFID readers which are pre-certified for key markets. CE marking for Europe and FCC approval for the US help to streamline international deployment.
It is also important to be aware of the cybersecurity and data privacy standards which apply locally, such as GDPR and NIS2 in the European Union and FERPA, HIPAA and NIST in the US. These standards affect the way that access data is collected, transmitted and stored, making secure credential handling and encrypted communication essential.
5: Evaluate total cost of ownership
When selecting an RFID reader, it is prudent to look beyond the advertised purchase price. The total cost of ownership includes not just the upfront hardware cost, but also the costs of installation, integration, and maintenance, as well as the scope to adapt the reader over time.
It is also important to take account of the cost of the credentials themselves: cost calculations must include both the reader and the associated credential technology, such as LEGIC, LEAF, or MIFARE, which can vary greatly in price and licensing structure. Choosing a reader designed for longevity and flexibility can save considerable time and money in the future.
A reader which cannot be updated or reconfigured may require full replacement or expensive on-site technician time when credential types, regulations or integration need to change. By contrast, a reader with remote update capabilities and flexible software settings can extend its useful life, reducing long-term costs and minimizing disruption.
6: Plan for scalability and future flexibility
The ideal RFID reader should be able to grow over time as the needs of the application change. Flexibility is useful as much for a phased roll-out across multiple locations, as for expansion of a unified access system, or the implementation of new infrastructure, credential types or security requirements.
Readers should be capable of being reconfigured to support new credential technologies, such as mobile access via Bluetooth or NFC, without requiring hardware replacement. Scalable readers reduce long-term costs, support evolving access strategies, and ensure that an access control solution stays up to date in a rapidly changing environment.
Future-ready readers should offer:
- Robust software support: a full-featured software development kit enables integration into diverse systems and supports the addition of new functionality over time, from credential recognition to device behavior.
- Configurable firmware: readers with flexible firmware can be adapted for new use cases, security requirements, or credential types, without the need for custom hardware.
- Remote update capabilities: remote management allows the deployment of firmware updates, reconfigured settings, or the roll-out of new features across distributed devices without manual intervention, saving time and reducing downtime.
- Credential flexibility: readers which can change or add new credential types can evolve with a changing ecosystem, cyber requirements and modernization.
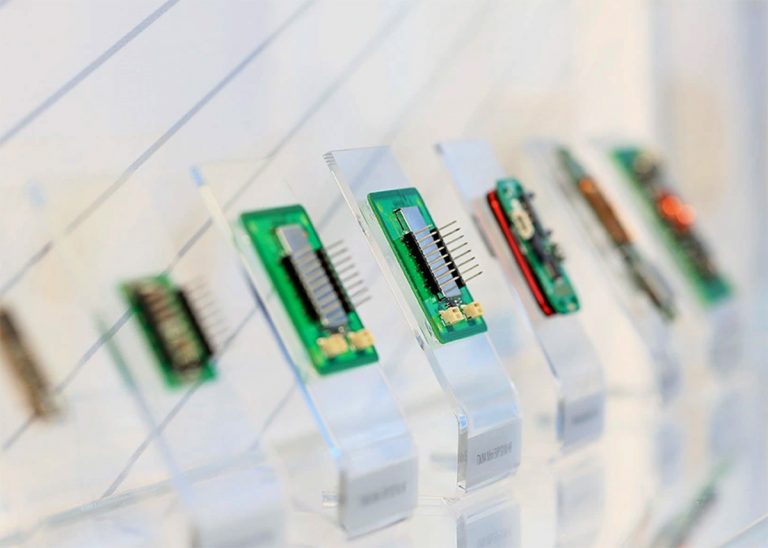
Universal RFID readers from ELATEC: flexible and future-ready
The latest universal RFID readers from ELATEC simplify access control while expanding the potential to add new security and convenience features. A universal RFID reader enables broad compatibility across technologies, systems, and geographies rather than locking the operator into narrow use cases or single-credential ecosystems. This results in easier integration, fewer part numbers to manage, and a clear path forward as credential standards and security needs evolve.
It also enables a unified access environment which brings physical and digital access together for better security, a smoother user experience, and easier system management.
The TWN4 family of RFID readers from ELATEC offers a wide selection of universal, technology-agnostic readers for almost any access application, backed by excellent software and service. The ELATEC universal TWN4 readers are:
- Technology-agnostic
- Mobile-ready
- Globally certified
- Easy to integrate
- Secure
- Configurable
- Future-ready
ELATEC technologies are designed for interoperability, and are not bound by a single credential platform or vendor ecosystem. That means more freedom, more flexibility, and fewer limitations as the system evolves.